Prove your AI controls are working — with evidence, not promises
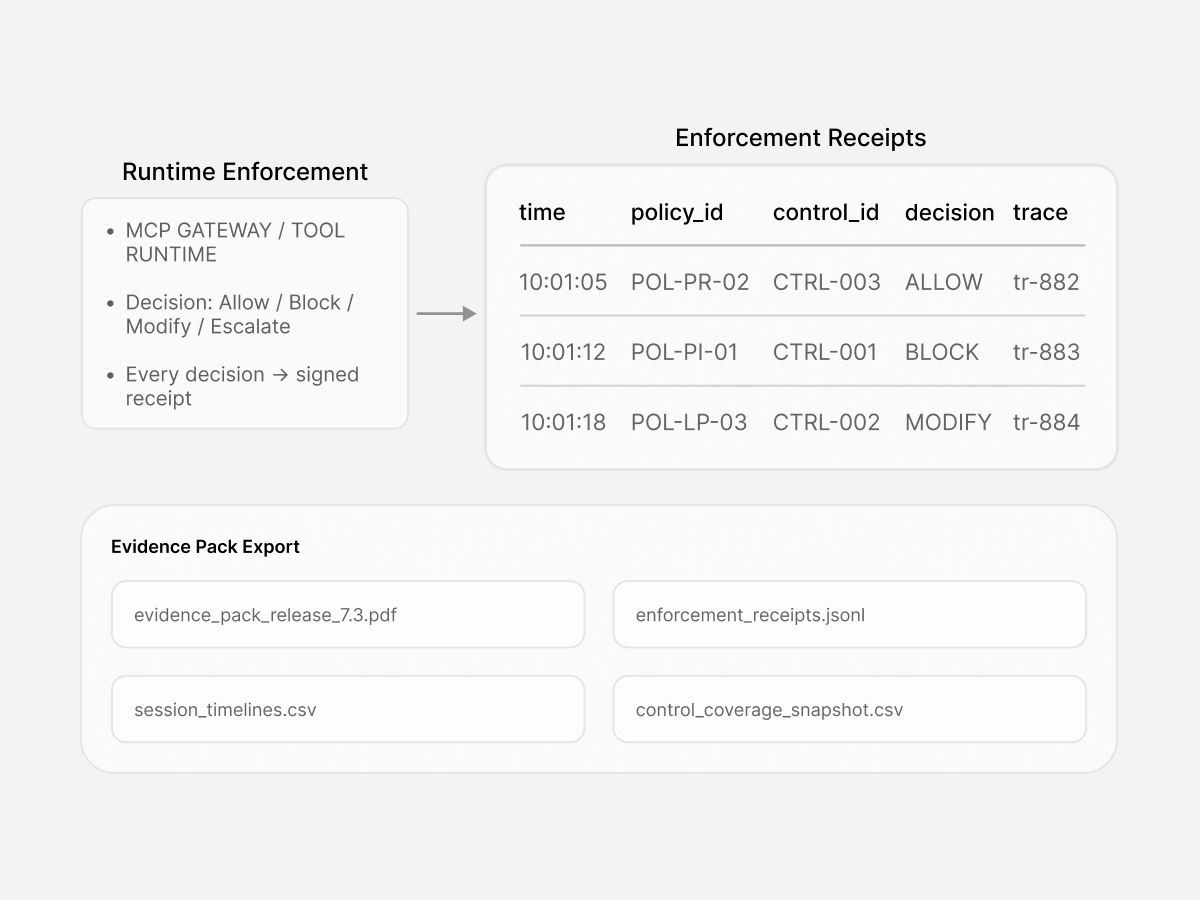
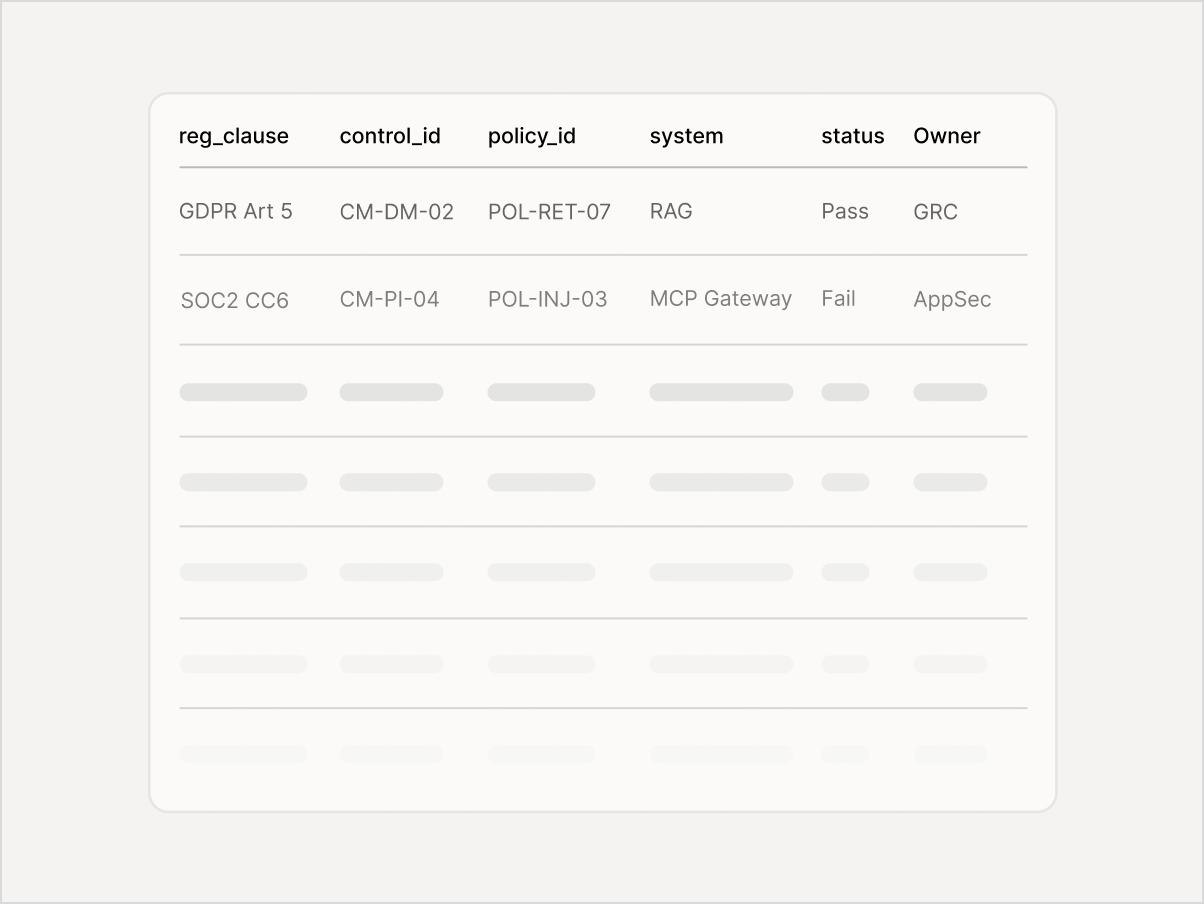
Turn policy into enforceable controls, validate them under real attack paths, and export an Evidence Pack whenever Security, Legal, or an auditor asks for it.

Launch blocked pending Security/Legal sign-off
Audit asks for evidence of AI controls
Procurement needs an AI risk attestation
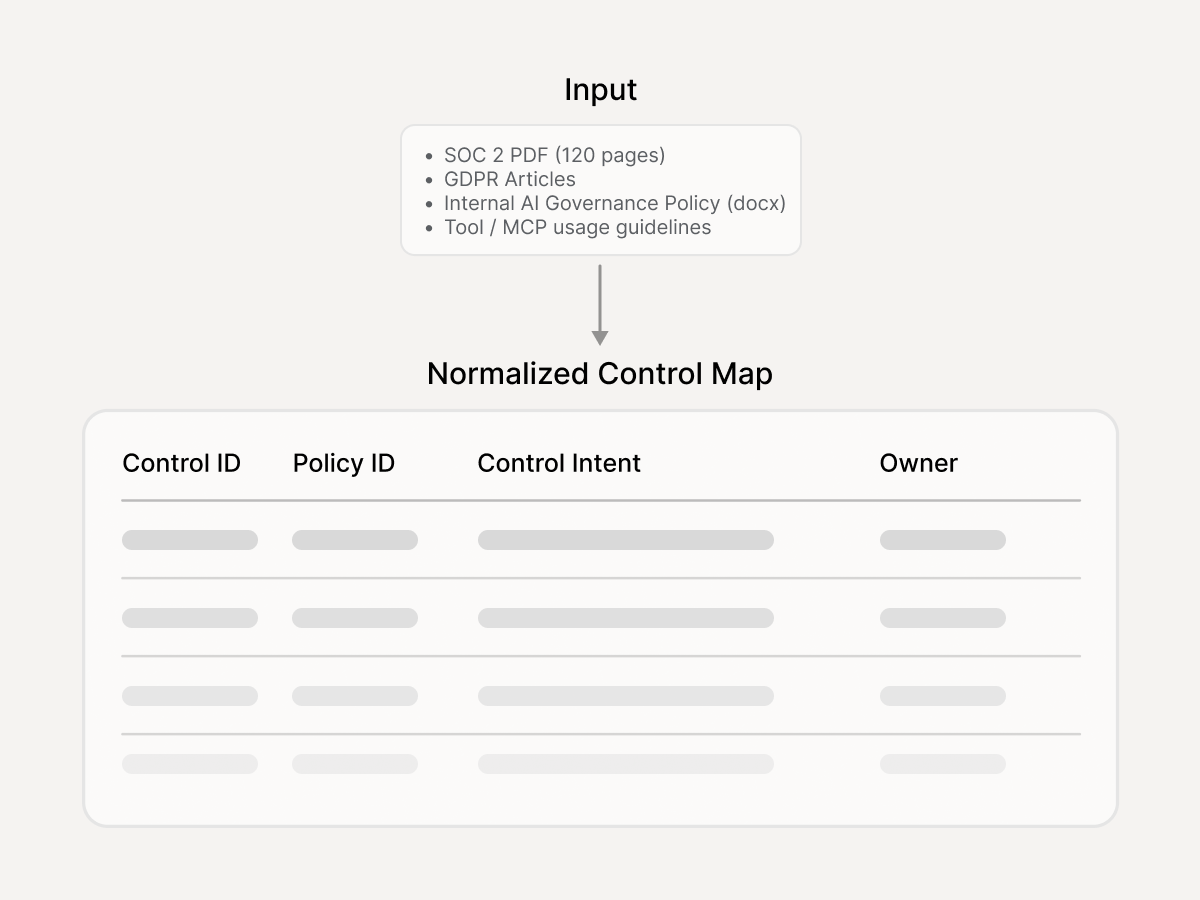
Three things you need to make compliance real
Most AI compliance is a spreadsheet that proves nothing. Enkrypt AI makes it provable.

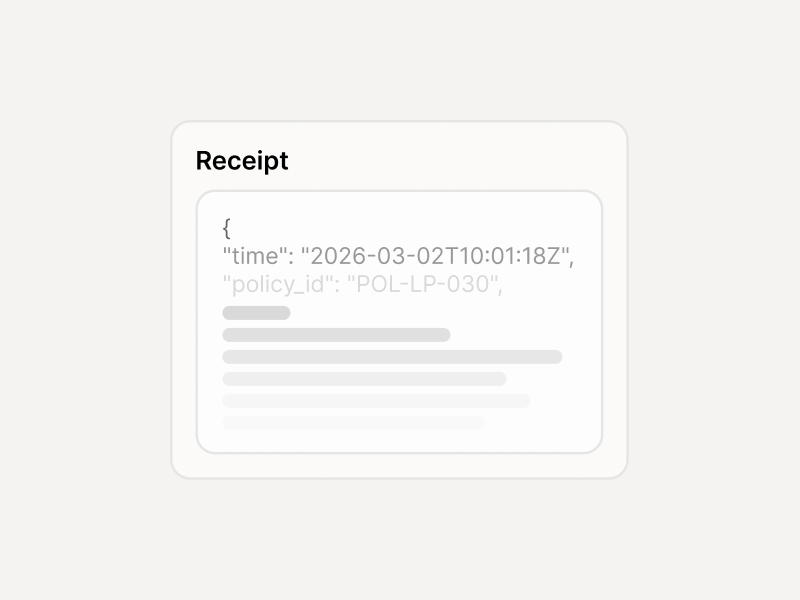
The Evidence Pack - one forwardable artifact
Everything Security, Legal, and auditors need to sign off — generated from real controls, real validation, and real runtime decisions.
Why Enkrypt AI
Most compliance tools generate paperwork. Enkrypt AI generates evidence from real controls enforced under real attack paths.
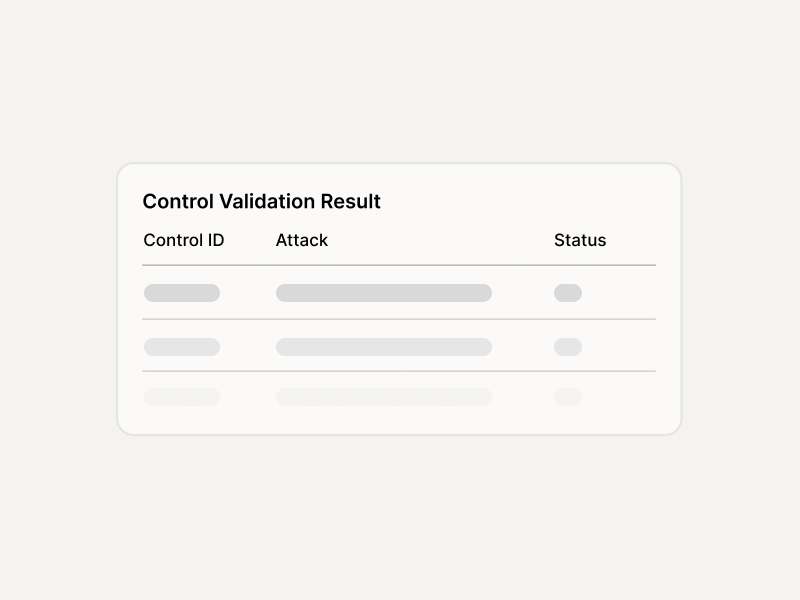
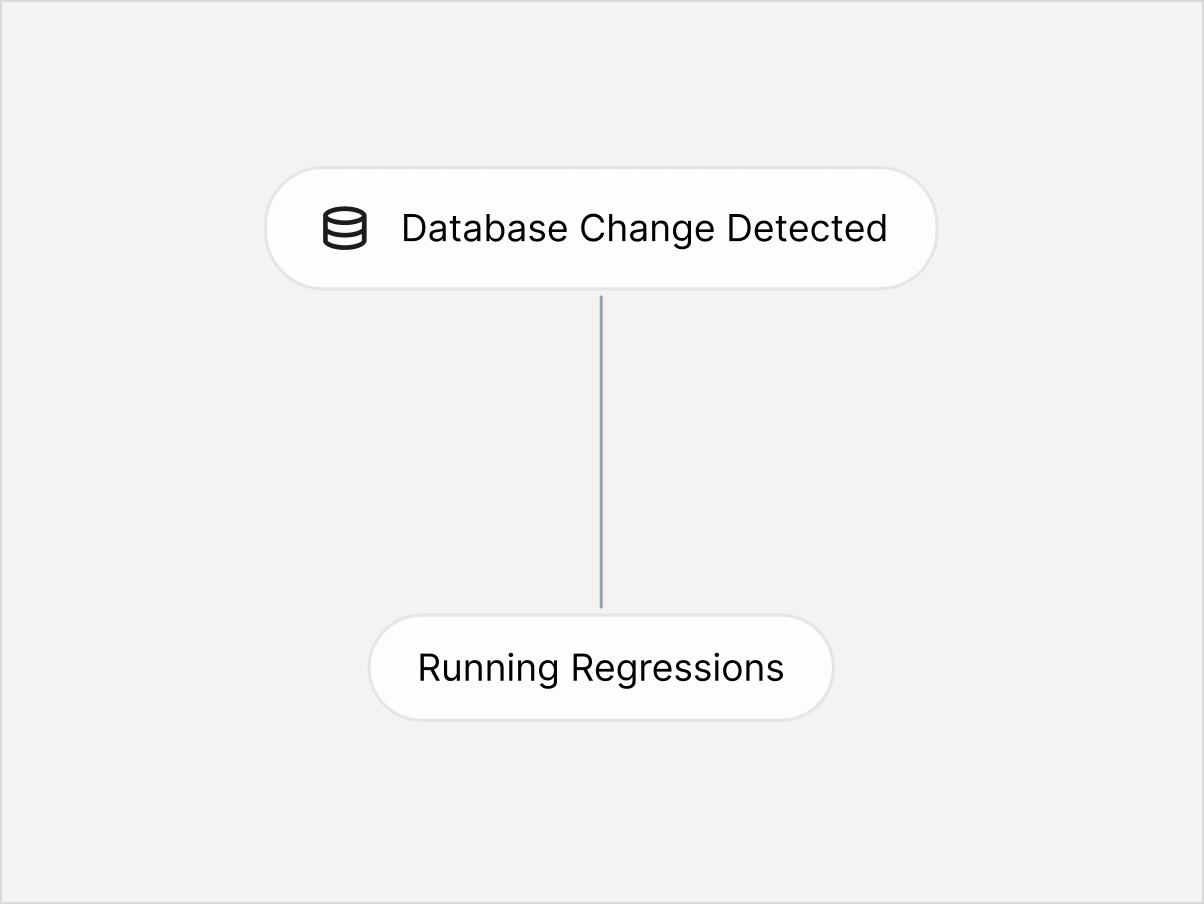
Controls aren't just documented — they're tested under adversarial conditions and pinned as regressions that run with every release.
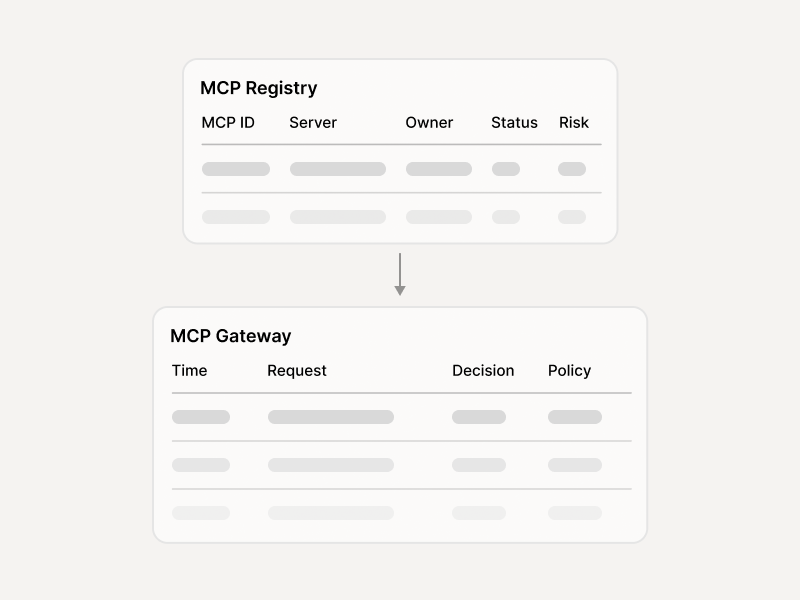
MCP Scanner and Gateway enforce allowlists, approvals, and traceability exactly where audit coverage matters most.
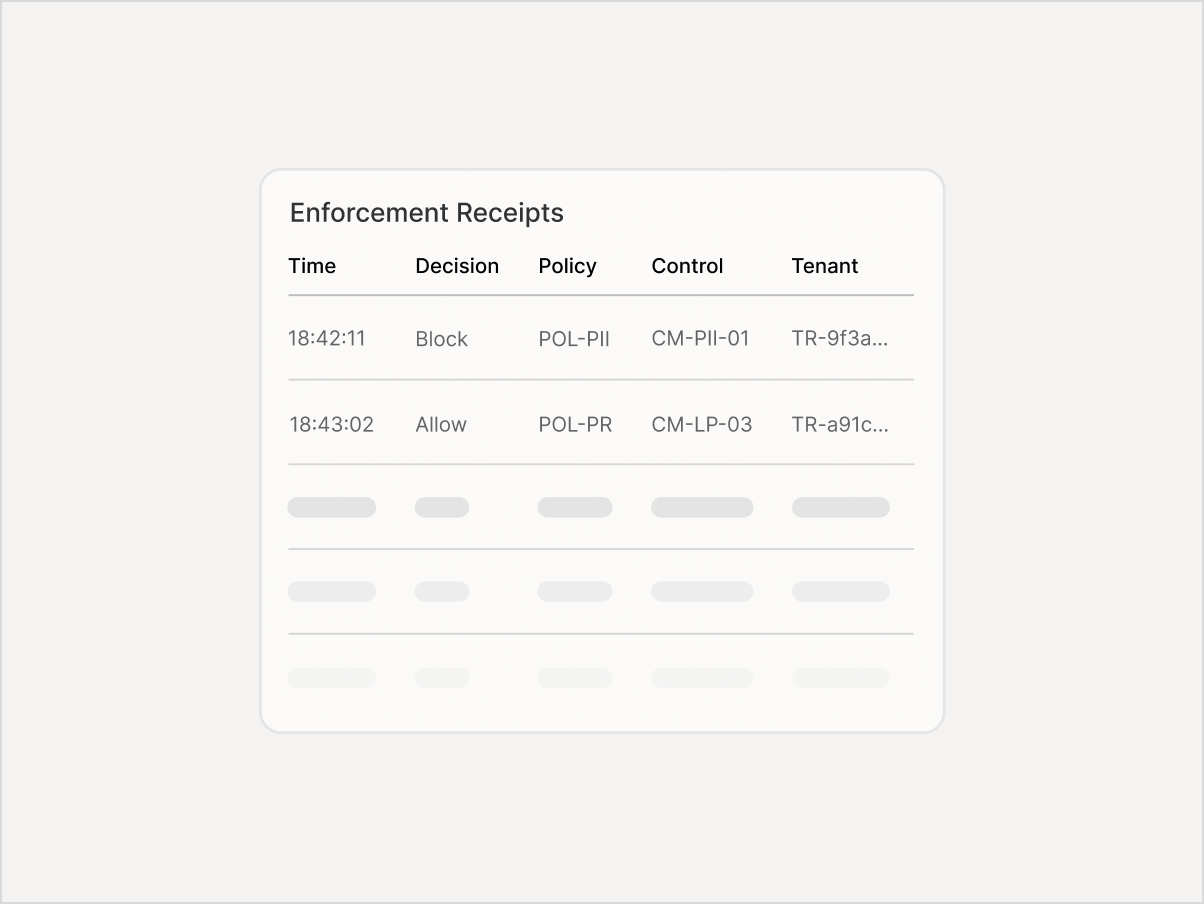
Every enforcement decision exports with policy ID, reason code, and trace ID — structured for auditors, not just for monitoring screens.
How teams use it
Whether you're unblocking a launch, surviving an audit, or gating releases — same platform, same evidence.
Built on five Enkrypt AI products
Each product handles one part of the compliance pipeline. Together, they produce the Evidence Pack.
Integrations
Compliance evidence and alerts flow into the tools your GRC, security, and engineering teams already use.
- Jira
- ServiceNow

- Splunk/ Sentinel/ Datadog
- Webhooks

- Slack
- Teams