Roll out MCP across your enterprise - without losing control
Scan MCP servers for vulnerabilities, approve what's trusted, assign by project, and enforce guardrails at runtime. No tool sprawl. No shadow adoption.
MCP is powerful. Unmanaged MCP is a liability.
Developers are connecting MCP servers to agents — but without visibility, approval workflows, or enforcement, every new tool is an uncontrolled access point.
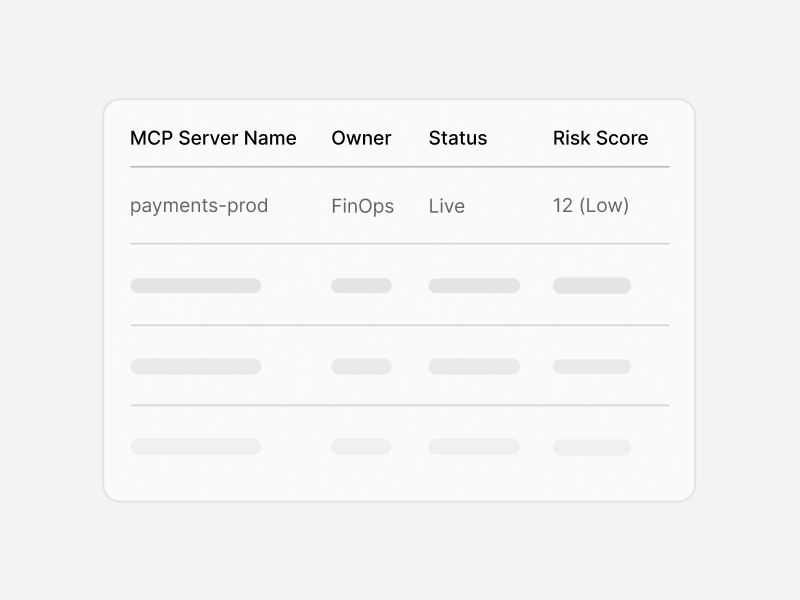
Developers install MCP servers without security review. You have no inventory, no risk scores, and no idea which tools have access to sensitive data or actions.
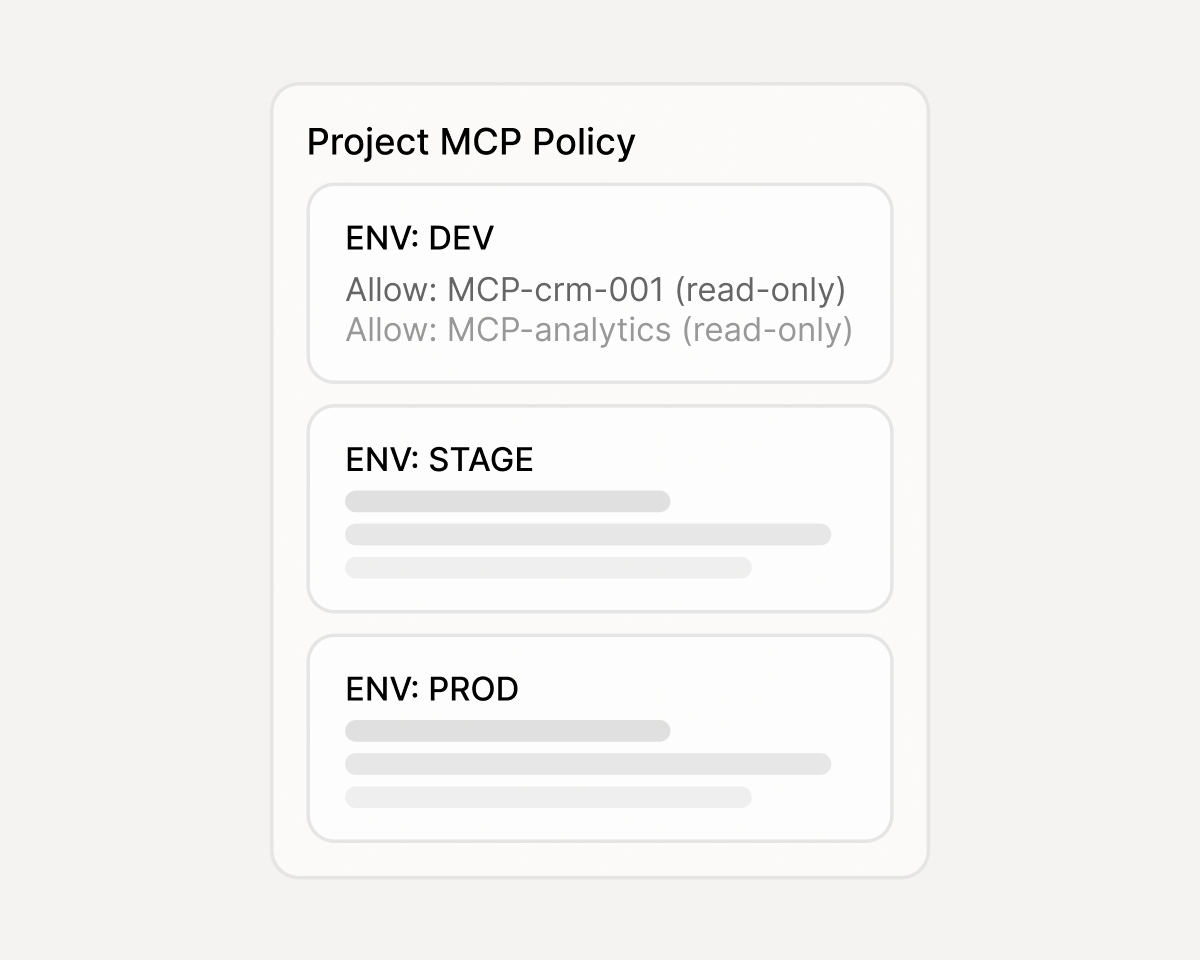
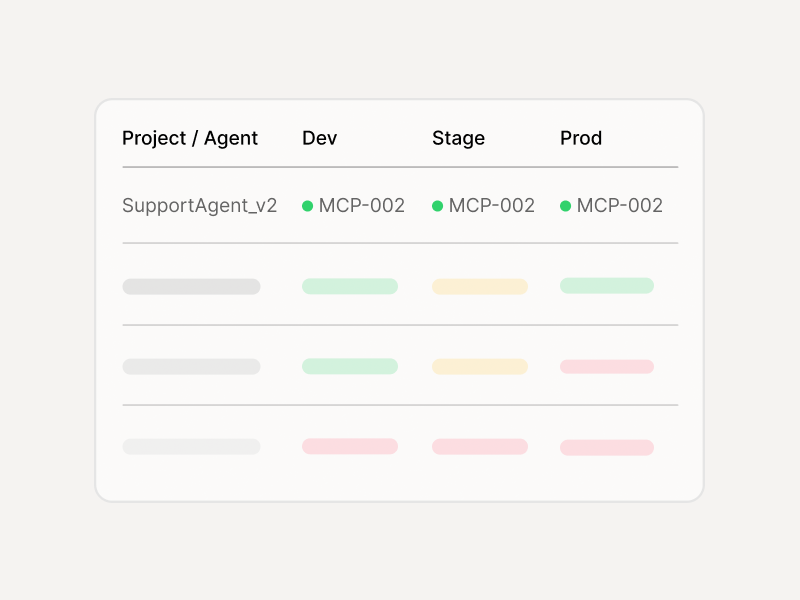
No per-project or per-environment allowlists. A dev agent and a production agent have the same MCP access — violating least privilege from day one.
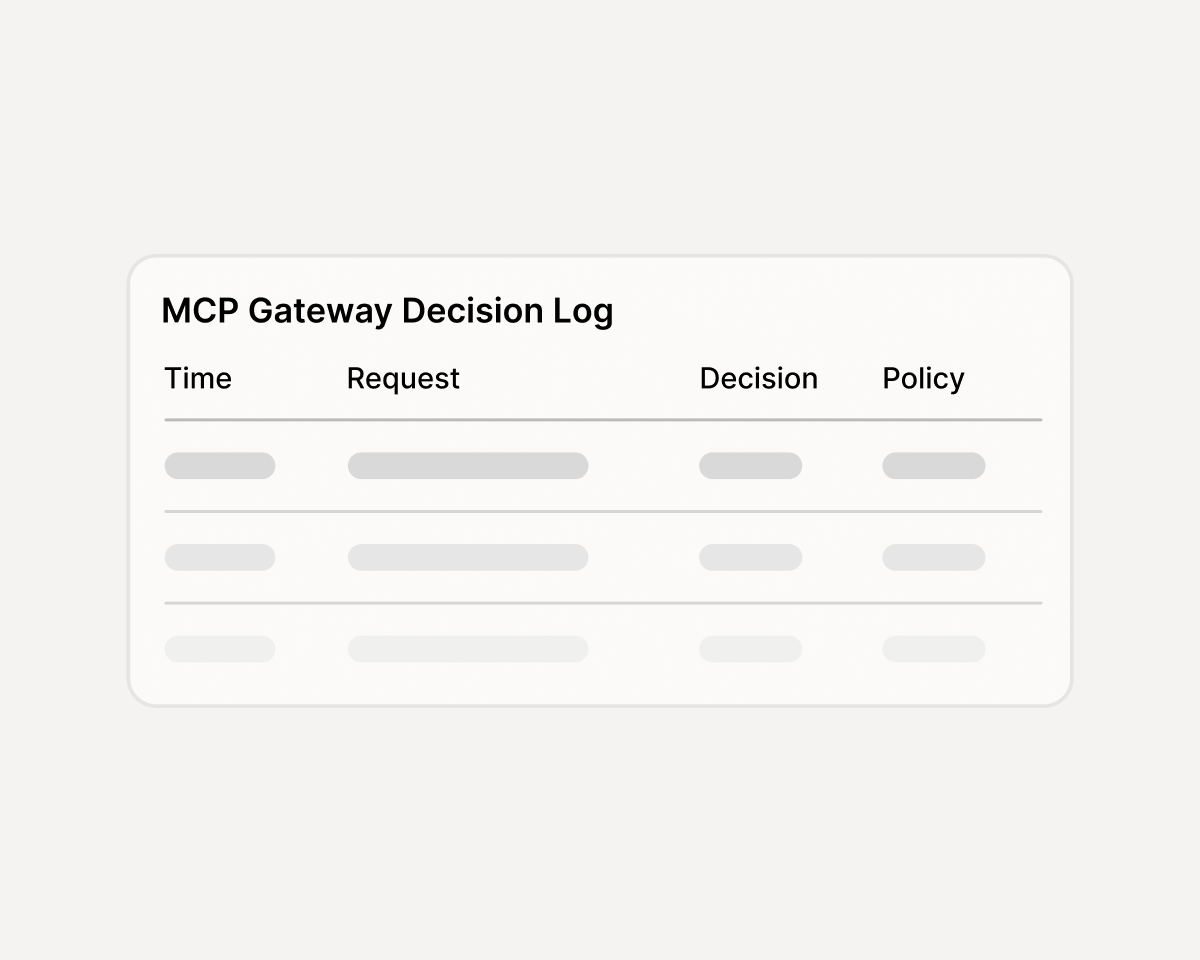
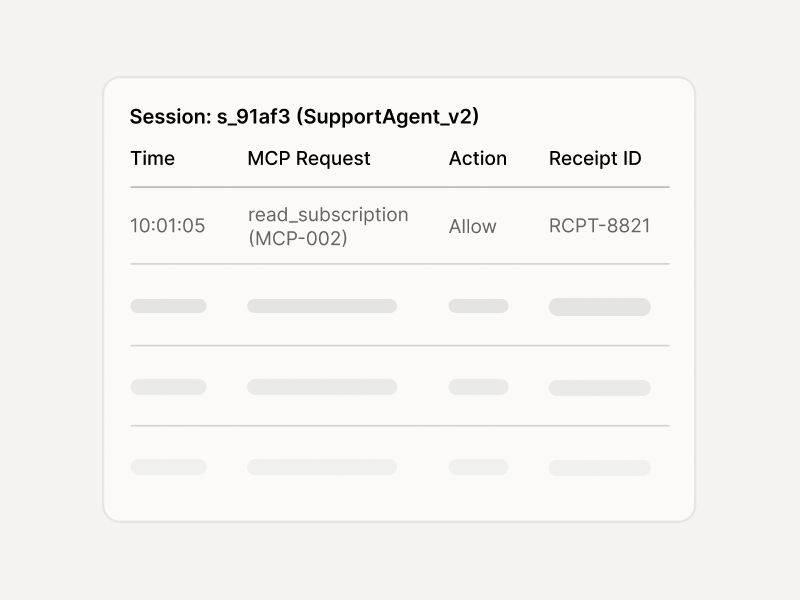
Tool calls happen at runtime with no policy layer. If an MCP server is misused, exploited, or leaks data, there's no log of what was allowed or why.
Scan. Curate. Configure. Enforce.
Four steps to make MCP governable - from first scan to production enforcement.

What you have in 30 days
Start with your top 10 MCP servers. Expand from there.
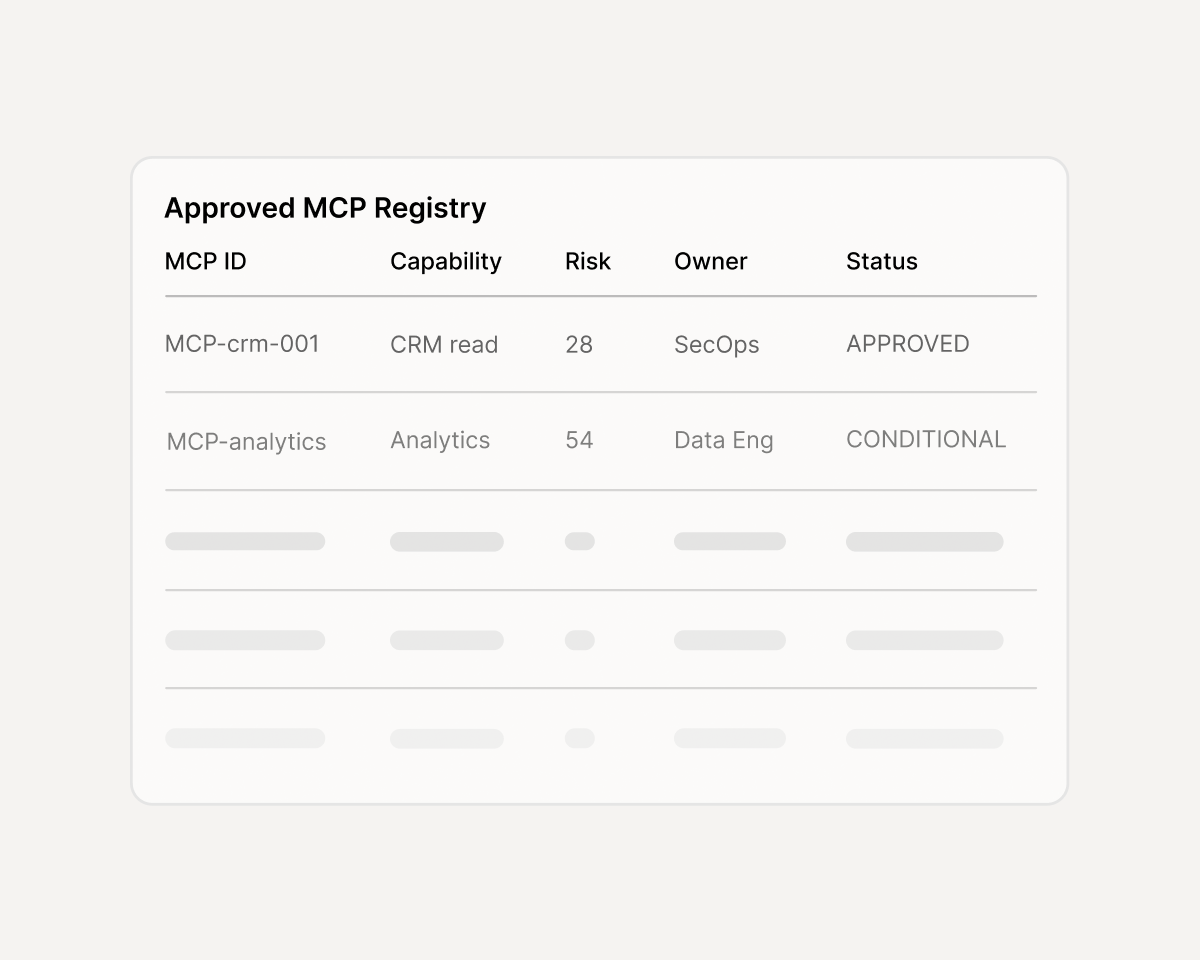
A central catalog of every trusted MCP server — with owners, risk scores, and metadata. No more shadow tools.
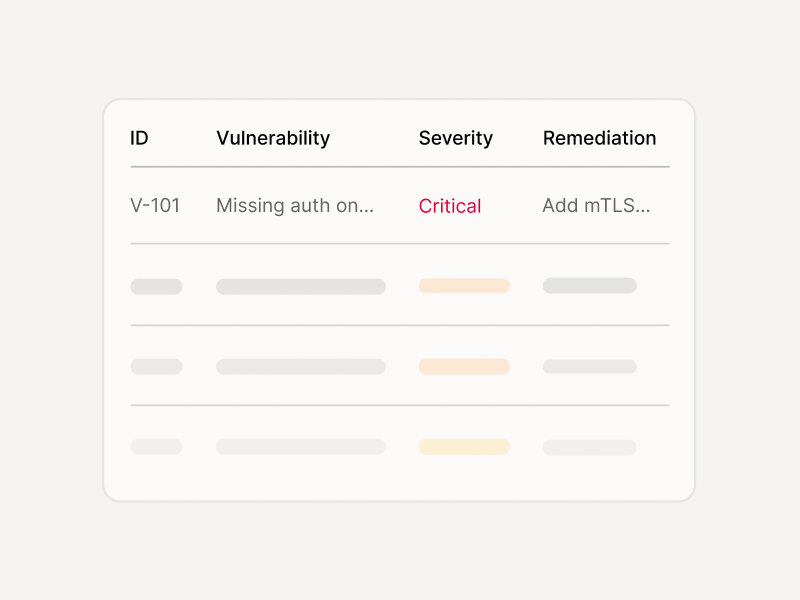
Vulnerability findings with severity, proof-of-concept, and remediation guidance for every scanned MCP server.
Per-project, per-environment MCP policies — dev, stage, and prod each get exactly the tools they need.
Every tool call gated by policy — blocked, modified, or approved — with receipts and trace logs.
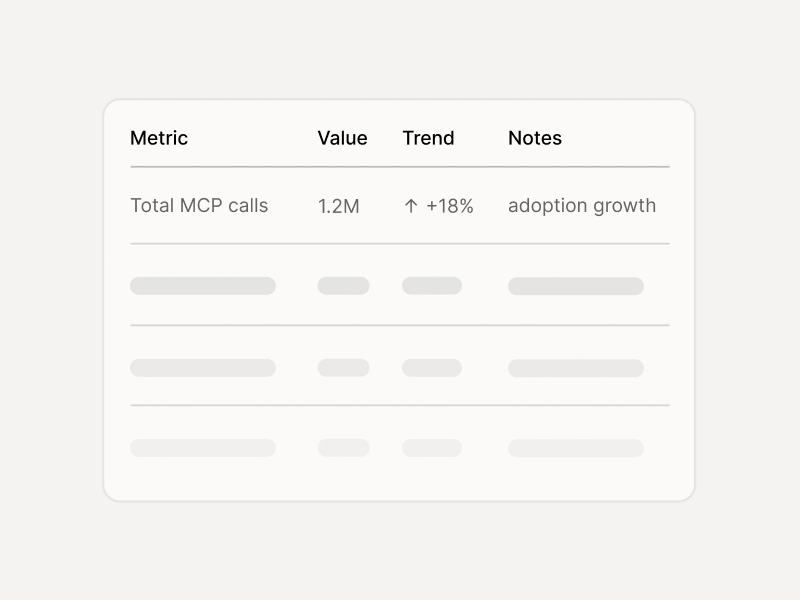
Traffic volumes, risk events, and configuration drift across all agents and environments — no log hunts.
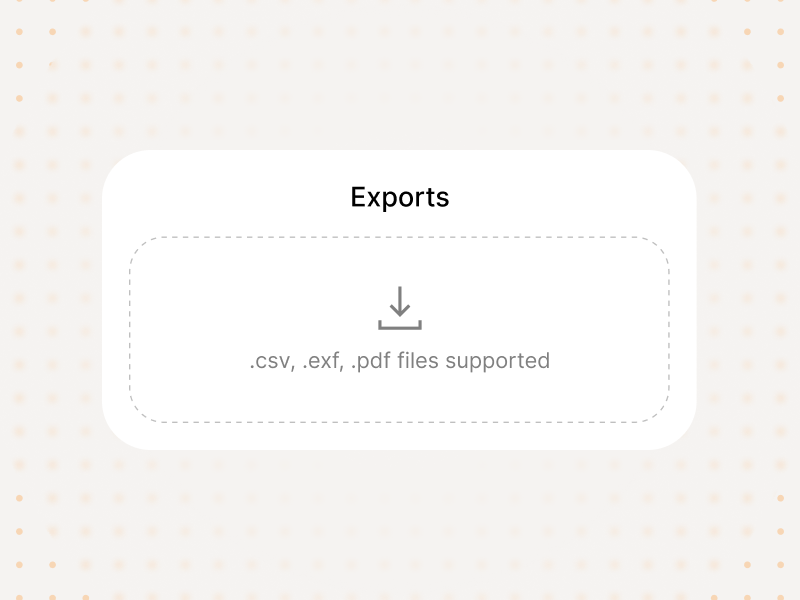
PDF, CSV, and JSON exports for compliance reviews, incident investigations, and retention requirements.
Six MCP attack vectors - covered
Each of these has been demonstrated in production MCP deployments. Enkrypt AI blocks them at the tool boundary.
Prompt injection tricks the agent into calling tools with attacker-controlled parameters.
Agent accesses tools or actions beyond its intended scope through tool chaining or parameter manipulation.
Sensitive data extracted through MCP tool responses, connector abuse, or outbound parameter encoding.
Malicious MCP server returns crafted responses that hijack the agent's reasoning loop.
Unapproved MCP servers connected by developers bypass security review and enter production undetected.
MCP configurations diverge between dev, stage, and prod — creating untested attack surfaces in production.
Start open source. Scale with enterprise.
Use the open-source gateway to deploy MCP controls today. Add Enkrypt AI when you need policy packs, audit exports, and expert security reviews.
Integrations
MCP security events flow into the tools your teams already use — alerts, workflows, SIEM, and exports.
- Slack / Teams
- PagerDuty / Opsgenie

- Jira
- ServiceNow

- Splunk/ Sentinel/ Datadog
- Webhooks